IP reputation used to be something analysts checked manually when an alert looked suspicious. Today, it’s a decision engine, quietly influencing what gets blocked, escalated, or ignored across the security stack.
At its core, IP reputation answers a simple question: Should this IP be trusted right now?
The difficulty lies in answering that question quickly, consistently, and with enough confidence to automate.
Legacy tools often struggle here. Aggregated platforms like VirusTotal return dozens of disconnected signals that require human interpretation. Modern SOCs don’t have time to analyze the analysis.
Where IP Reputation Delivers the Most Value
Stopping Malicious Traffic Before It Spreads
At the network edge, IP reputation functions as a real-time filter. Firewalls, secure web gateways, and DNS-layer controls rely on reputation scores to decide whether traffic should ever reach an endpoint.
When IP reputation data is high confidence and continuously updated, security teams can block active command-and-control servers, phishing hosts, and malware infrastructure without waiting for signatures to catch up. This dramatically reduces MTTD and limits blast radius from early detection.
Making SIEM Alerts Worth Investigating
In most SIEM environments, the problem isn’t a lack of alerts, it’s that too many alerts look the same. IP reputation changes that by adding context at ingest time.
When logs are enriched with a clear IP risk score and supporting context, analysts immediately understand which events deserve attention. An authentication attempt from a high-risk hosting provider probably doesn’t get treated the same as one from a residential ISP.
Platforms like Splunk become more actionable when good threat intelligence turns raw IP telemetry into prioritized signals.
Powering SOAR Decisions Without Human Bottlenecks
Automation only works when inputs are consistent. That’s why IP reputation is foundational to SOAR platforms such as Tines and Swimlane.
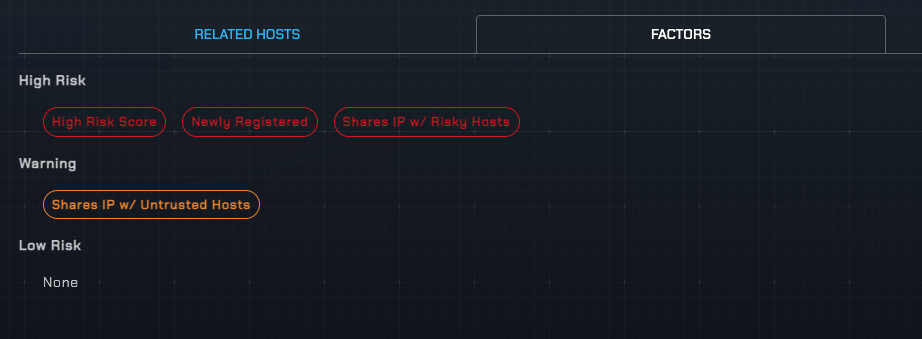
When an IP exceeds a defined risk threshold (ours run from 1.00 to 10.0), playbooks can automatically block it, enrich the case with passive DNS and GeoIP context, or escalate the incident—all without waiting for an analyst to reconcile conflicting verdicts.
The key difference is explainability. Automation breaks down when reputation data can’t justify its own conclusions to a human.
Exposing Phishing and Malware Infrastructure Earlier
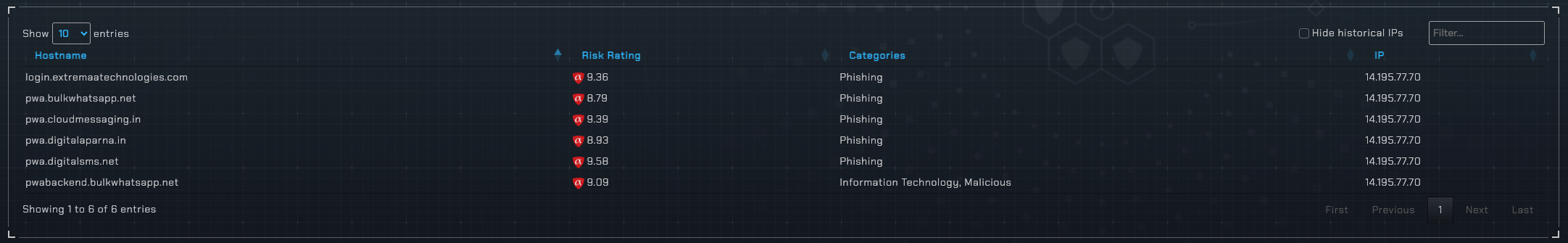
Attackers rarely build infrastructure from scratch for every campaign. They reuse hosting providers, rotate IPs within familiar ranges, and lean on the same ASNs. (You can read our research on high-risk ASNs.)
Advanced solutions recognize these patterns. Even if a domain is brand new, its IP-level relationships often reveal risk immediately. This is especially valuable for phishing detection, where speed matters more than volume.
Email security teams and MDR providers use IP reputation to catch campaigns while they’re still forming, not after they’ve already landed in inboxes.
Reducing Fraud Without Breaking User Experience
Outside the SOC, IP reputation plays a quieter but equally critical role in fraud prevention. Login abuse, account takeovers, and automated bot traffic often originate from infrastructure with long histories of misuse.
Rather than hard-blocking users, organizations can apply adaptive controls, adding friction only when the risk justifies it. The result is lower fraud rates without unnecessary customer frustration.
Enabling Security Products, Not Just Security Teams
For vendors building security products, IP reputation is an embedded capability and competitive advantage.
OEMs and platforms need reputation data that’s API-first, high volume, and consistent enough to expose directly to customers. A single, scored verdict backed by human-readable threat factors is far easier to integrate than a bundle of raw engine results.
This is where purpose-built threat intelligence outperforms crowdsourced sources designed for manual research.
What Separates Strong IP Reputation From Noise
Not all IP reputation is created equal. The most effective solutions share a few defining traits: real-time updates, a clear risk score, and contextual intelligence that explains why an IP is dangerous.
Our approach to IP reputation focuses on high-fidelity verdicts, contextual reasoning, and automation-ready APIs, making it suitable for SOCs and security products alike.
IP Reputation as a Force Multiplier
When implemented correctly, IP reputation doesn’t just block bad traffic—it improves everything downstream. Alerts become clearer, automation becomes safer, and analysts spend less time debating verdicts and more time stopping threats.
In modern security operations, this isn’t a lookup step. Rather, it’s the foundation that makes fast, confident decisions possible.
Need better IP reputation in your SOC or product? Request your free trial of the alphaMountain API and we’ll get you started right away.