Threat intelligence platforms are only as good as the intel flowing into them. You can have the cleanest workflow, the sharpest analysts, and the most elegant investigation UX — but if your IOC data is stale, incomplete, or stripped of context, you’re making decisions on sand.
Today, we’re announcing a native integration between alphaMountain and Morado’s Threatnote. Threatnote users now get alphaMountain threat intelligence directly inside their TIP — no export/import cycle, no context switching, no stitching together data from a dozen browser tabs. Two tiers. One clean integration.
What Morado’s Threatnote Does
Threatnote is a threat intelligence platform built for operational security teams. It handles the full TI workflow: IOC collection, enrichment, investigations, taskings, hunting, and stakeholder reporting — all in one place. If you’re running a SOC or an intel operations function, it’s the kind of platform that replaces the folder of bookmarks and the shared spreadsheet that has become load-bearing infrastructure.
The integration with alphaMountain makes it substantially more powerful for any team that needs to know right now whether a domain or URL is worth acting on.
Two Tiers of Integration
Tier 1: Community 1000 — Free for Every Threatnote Customer
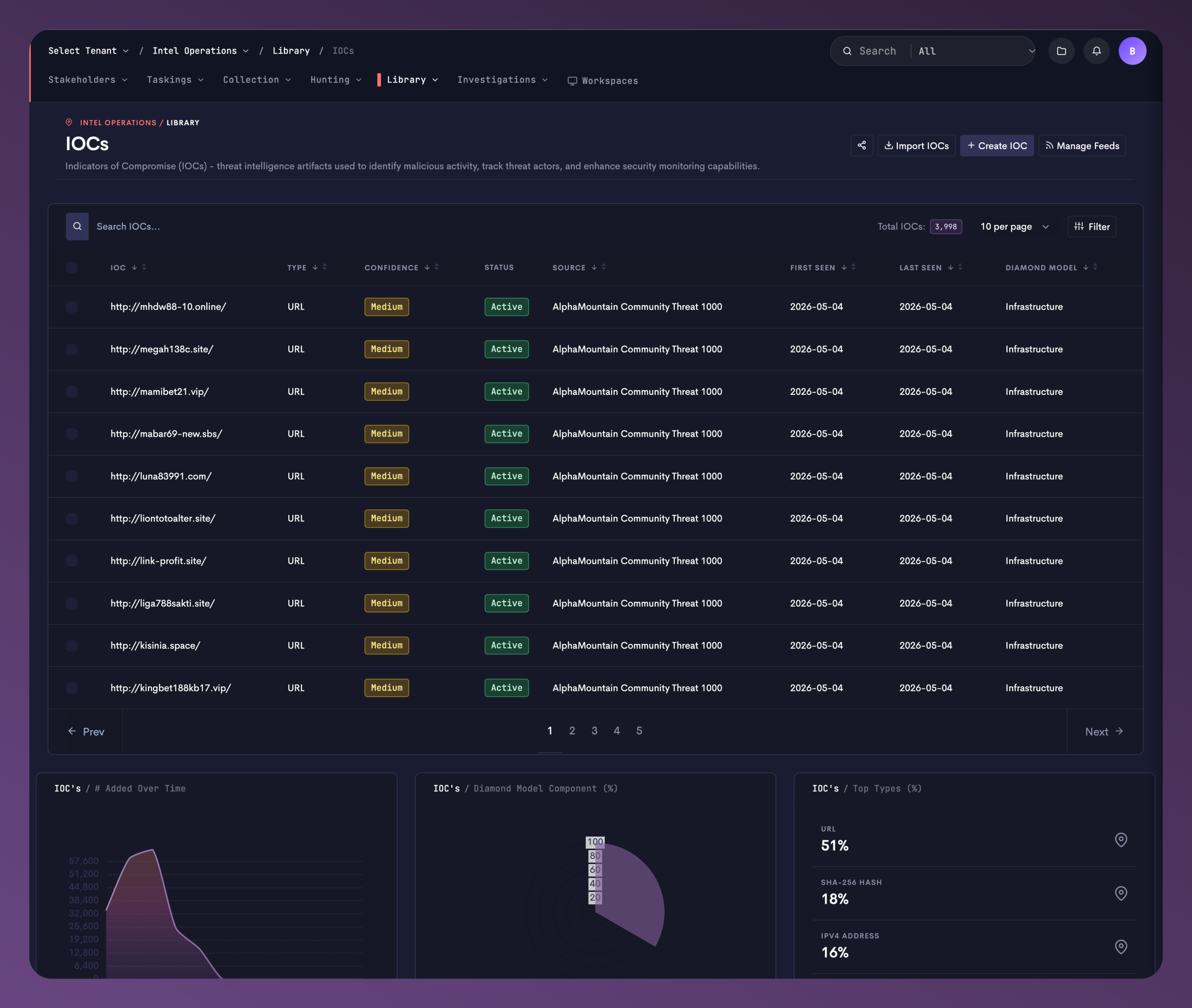
Every Threatnote customer gets the alphaMountain Community Threat 1000 feed out of the box, at no additional cost.
The Community 1000 is a continuously-refreshed selection of recent risky URLs and domains from alphaMountain’s dataset. These aren’t aged blocklist entries — they’re active, current threats, sourced and scored using the same AI engine that powers the full aM Intelligence™ API. IOCs are mapped to the Infrastructure component of the Diamond Model and marked active at time of ingestion.
Inside Threatnote’s IOC Library, these come in pre-labeled as AlphaMountain Community Threat 1000, so your team knows exactly where each indicator originated. You’ll see the source attribution on every IOC row — no ambiguity about data provenance, which matters when you’re making block decisions or briefing stakeholders.
Tier 2: Full aM Intelligence™ — Bring Your Own Key
If you have an alphaMountain license, you unlock the full enrichment layer. This is where the integration goes from useful to genuinely powerful.
Request a free alphaMountain API trial →
When you pull up any IOC in Threatnote, a dedicated AlphaMountain tab appears in the detail view alongside your other enrichment sources (VirusTotal, URLScan.io, AlienVault, ThreatFox, Whois). That tab surfaces the complete aM Intelligence™ dataset for the indicator — all of it, directly in context.
Here’s what’s included:
DGA Probability. A domain that looks random might be random for a reason. alphaMountain’s DGA (Domain Generation Algorithm) scoring gives you a precise probability that the domain was machine-generated by malware — not a binary flag, an actual decimal score. For f0rmate.para5itrecal.in.net, the domain probability is 0.00039 and the hostname probability is 0.013. Low DGA scores don’t mean the domain is safe — they just mean it wasn’t algorithmically generated. The risk summary tells the rest of the story.
Risk Summary. Every enriched IOC gets a tiered risk breakdown: High Risk factors, Mid Risk factors, and Low Risk factors — with specific labels attached to each. In the screenshots: “Unpopular Site,” “Possibly Unsafe TLD,” “Host on Untrusted IP.” These aren’t black-box outputs. Your analysts can see exactly what drove the risk assessment, which means they can explain it — to incident response, to the CISO, to a client.
DNS, Geo, and Passive DNS. Current DNS records plus passive DNS history. Where has this domain resolved over time? What nameservers is it using? Geo context for the resolved IPs. This is the kind of data that turns a single IOC into a map of infrastructure.
Popularity. Is this domain in the top 1 million? Unranked entirely? Domain popularity is a fast signal — a newly registered, unranked domain requesting corporate credentials isn’t subtle.
WHOIS. Registration dates, registrar, registrant — embedded in the enrichment view, no separate lookup required.
AI Summary. Threatnote surfaces an AI Summary button on every alphaMountain-enriched IOC. One click, and the full enrichment dataset gets synthesized into a human-readable assessment. Useful when you’re triaging at volume and need a fast read before diving into the data.
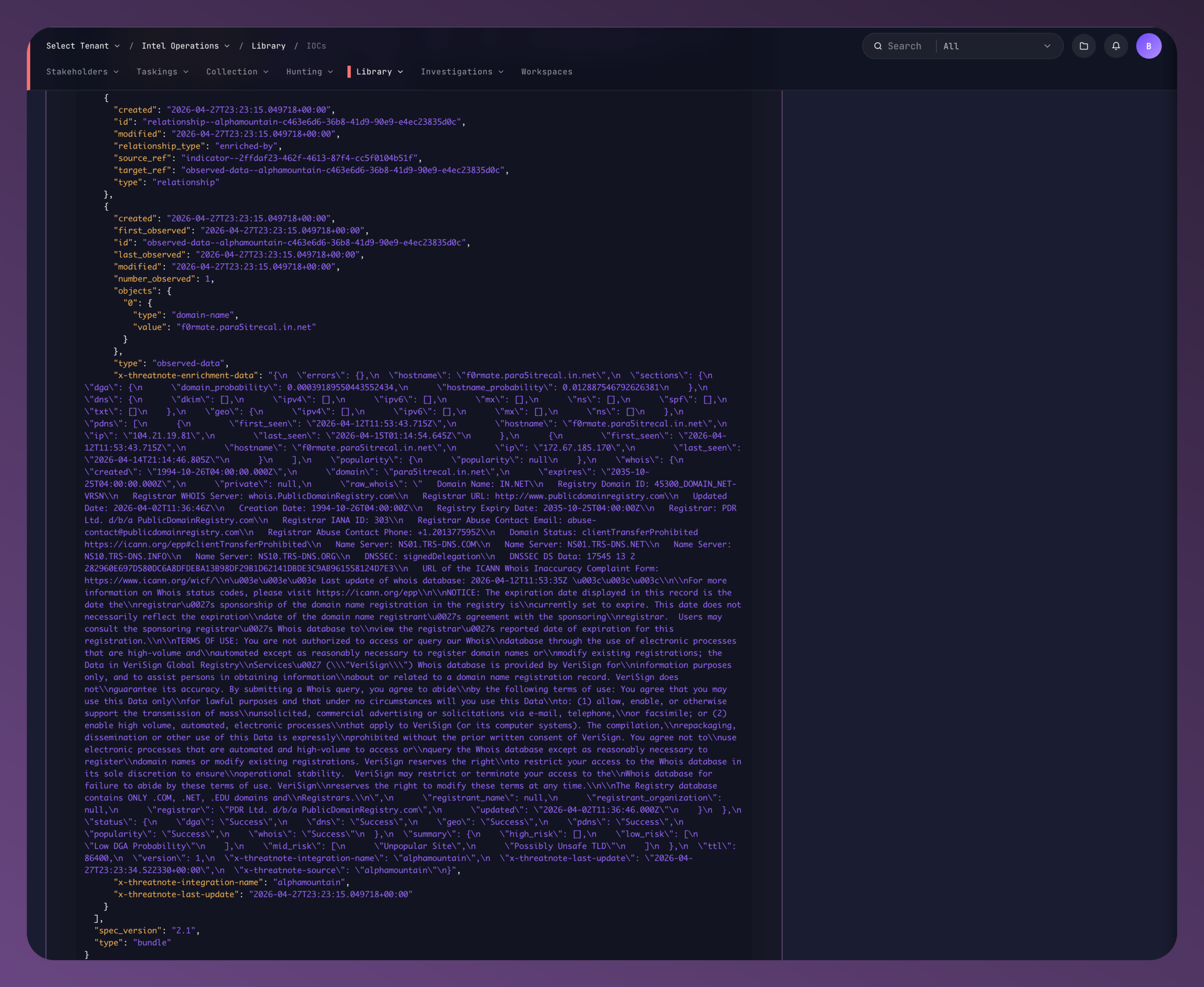
All of this enrichment flows in as STIX custom extension data (x-threatnote-enrichment-data), keeping your IOC objects standard-compliant while carrying the full alphaMountain intelligence payload.
IOC Lifecycle, Not Just IOC Ingestion
One thing the Threatnote integration does particularly well: it respects IOC lifecycle. The platform’s Decay Timeline shows you where each IOC sits in its confidence arc — Active, High, Medium, Low, Aged Off — with specific date milestones for each transition. When you combine that decay model with alphaMountain’s hourly-updated enrichment, you get intelligence that degrades gracefully instead of going stale without warning.
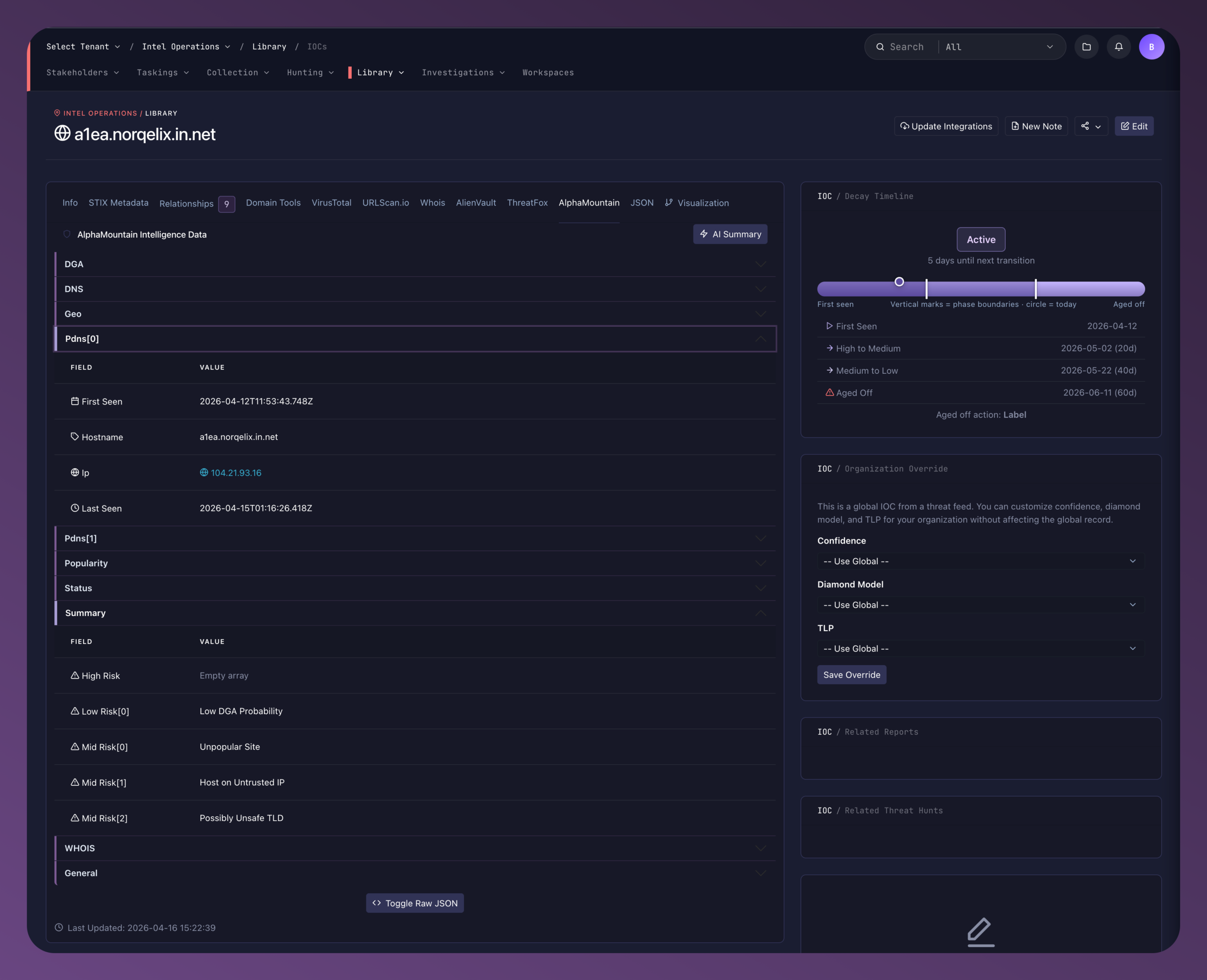
You also get per-organization override controls. Want to dial up the confidence on a specific IOC without affecting the global record? Adjust the Diamond Model classification? Change TLP? Threatnote lets you do that at the organization level, preserving the integrity of the shared feed while letting your team annotate for your context.
Who This Is For
If you’re running Threatnote today without an alphaMountain integration, the Community 1000 feed is already in your platform. Turn it on.
If you’re working investigations that require more depth — full infrastructure context, DGA scoring, passive DNS history, the complete enrichment picture — talk to us about an aM Intelligence license. The difference between “this URL scored high risk” and “this URL is an unpopular site on an untrusted IP with a possibly unsafe TLD, first seen 24 days ago, sharing infrastructure with these other hosts” is not a small difference. It’s the difference between a note in the ticket and an actionable block.
Already a Threatnote customer? The Community 1000 feed is included at no cost. Verify it’s active in your Library → Manage Feeds settings.
Need the full aM Intelligence layer? Start a free API trial → [email protected] or book time with sales → here.
New to alphaMountain? Start with threatYeti.com — free, no account required, and you’ll see the data depth firsthand.

