Most enterprise security teams have solid coverage on email attachments, credential harvesting forms, and malware downloads. What they tend to have less visibility into is what happens inside the SaaS platforms their marketing departments live in every day.
Meta Business Manager is one of those platforms. At any given enterprise, it’s being accessed by in-house marketing teams, external agencies, freelance contractors, and regional partners — each with varying levels of access to ad accounts, Pages, pixels, and payment methods. IT and security rarely have a seat at that table.
Threat actors know this. Which is why Business Manager account takeover campaigns are an increasingly attractive attack surface — and why we’re seeing infrastructure built specifically to exploit it.
We recently identified one. Here’s how it works.
The Bait
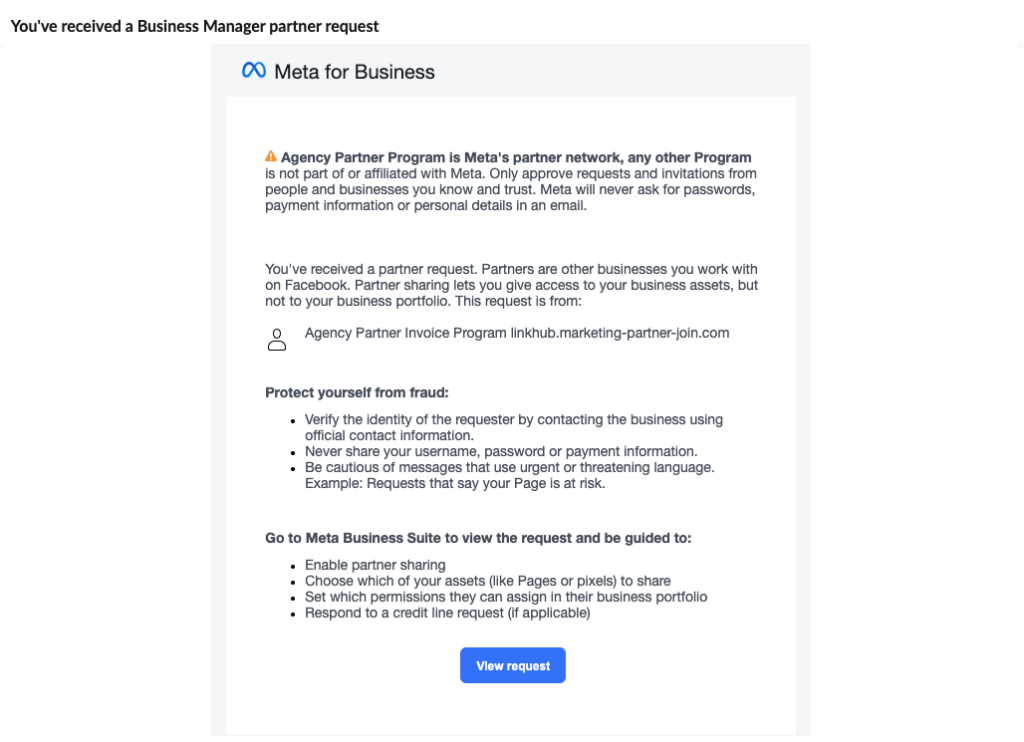
The attack arrives as a legitimate-looking email with the subject line: “You’ve received a Business Manager partner request.”
Fake Meta Business Manager partner request email from “Agency Partner Invoice Program” at linkhub.marketing-partner-join.com
The email is styled precisely like a real Meta for Business notification — correct branding, correct layout, correct CTA button labeled “View request.” Even the disclaimer language is lifted wholesale from Meta’s actual communications: “Agency Partner Program is Meta’s partner network, any other Program is not part of or affiliated with Meta.”
There’s a certain dark irony in a phishing email that warns you about phishing.
The request claims to be from “Agency Partner Invoice Program” and links to the domain linkhub.marketing-partner-join[.]com. The framing is designed to create low-friction urgency — businesses receive legitimate partner requests all the time, so the instinct is to click through and deal with it.
The domain name itself is doing real work here. “marketing-partner-join” sounds plausible enough to pass a quick glance. It doesn’t scream malicious — which is exactly the point.
Domain Intelligence
Running linkhub.marketing-partner-join[.]com through threatYeti tells a different story.
threatYeti scan results for linkhub.marketing-partner-join.com — Risk Rating 7.60, Category: Suspicious, registered April 16, 2026
Risk rating: 7.60 out of 10.00. Category: Suspicious.
The WHOIS creation date is April 16, 2026 — just two days before this post was written. That’s not a coincidence. Newly registered domains are a standard operational tactic: spin up infrastructure, detonate the campaign, and move on before threat feeds catch up. The domain has no certificate (unavailable), no popularity rank (not in the top 5 million sites), and resolves through Cloudflare — another common tactic to obscure origin infrastructure.
The Infrastructure
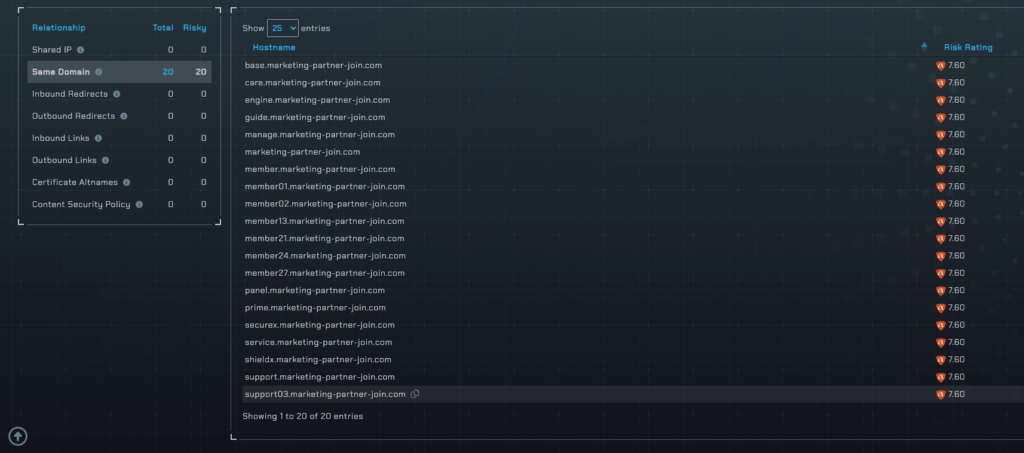
One newly registered suspicious domain is a red flag. Twenty is a campaign.
Same-domain related hosts for marketing-partner-join.com — all 20 subdomains rated 7.60
threatYeti’s related hosts module surfaces 20 subdomains under the same root domain — every single one rated 7.60. The subdomain naming convention is telling:
base.marketing-partner-join.companel.marketing-partner-join.commanage.marketing-partner-join.commember.marketing-partner-join.com/member01throughmember27securex.marketing-partner-join.comshieldx.marketing-partner-join.comprime.marketing-partner-join.comsupport.marketing-partner-join.com/support03
This is organized infrastructure. The member## pattern suggests victim or campaign tracking. The panel and manage subdomains suggest a backend control interface. The securex and shieldx naming may be designed to appear as security-related tooling to anyone who stumbles across them.
This isn’t a single throwaway phishing page. It’s a platform built to scale.
Risk Factors
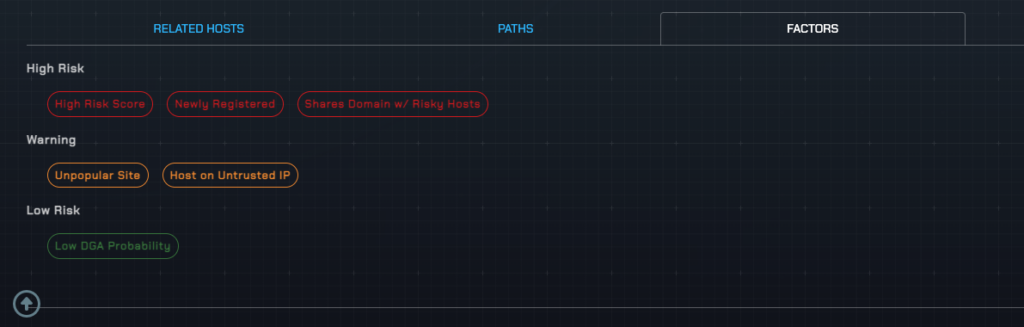
threatYeti risk factor breakdown — High Risk Score, Newly Registered, Shares Domain w/ Risky Hosts (High Risk); Unpopular Site, Host on Untrusted IP (Warning)
The risk factor breakdown from aM Intelligence™ tells the complete story:
High Risk: High Risk Score, Newly Registered, Shares Domain w/ Risky Hosts
Warning: Unpopular Site, Host on Untrusted IP
Low Risk: Low DGA Probability
The one “low risk” factor — low DGA probability — is actually consistent with how this campaign operates. It doesn’t need a domain generation algorithm because the operators registered the domains manually and deliberately. The names are constructed to appear legitimate at a glance. That’s a human choice, not an automated one.
What’s at Stake
For a single user who clicks through and approves the partner request, the attacker gains access to their business assets — ad accounts, Pages, pixels, and payment methods. But the blast radius at an enterprise level is considerably larger.
A marketing agency managing Business Manager access for 30 or 40 clients is a single point of failure. One approved partner request from one account manager could expose every client account under that agency’s portfolio. An enterprise with regional Business Manager hierarchies — each managed by a different team, each connected to shared brand assets — faces a similar exposure. The attacker doesn’t need to compromise every account. They just need one person to click “View request.”
Once in, the options are well established: drain ad budgets running their own campaigns on the victim’s dime, exfiltrate first-party audience data, hijack brand Pages, or sell the compromised access on the secondary market. Business Manager accounts with active payment methods and large audiences have documented resale value.
What makes this attack class particularly difficult for security teams is that it generates no traditional IOCs at the endpoint level. There’s no malware, no credential harvesting form, no suspicious file attachment. The entire compromise happens inside a legitimate platform’s permissions framework — invisible to email security, endpoint detection, and most SIEM alerting. By the time anyone notices something is wrong, the access has already been granted.
Detection
The upstream intercept point for a campaign like this is the link in the phishing email — and that’s exactly where domain-level threat intelligence earns its keep.
This campaign is engineered to evade legacy URL classification: a domain name that reads as legitimate, Cloudflare hosting that obscures true origin infrastructure, no malicious payload to scan, and a newly registered domain that hasn’t appeared on any blocklist yet. A static-database URL filter with daily update cycles won’t catch a domain that’s two days old.
aM Intelligence™ flagged marketing-partner-join[.]com and all 20 of its subdomains at a risk rating of 7.60 within days of registration — before any other source had it classified. A secure email gateway, secure web gateway, or DNS filter running aM Intelligence™ would have blocked the link in this phishing email before it reached the inbox of a single marketing manager, agency employee, or contractor.
For security teams responsible for protecting environments where SaaS platform access is distributed across departments, agencies, and external partners, the detection surface for this attack class is narrow: it’s the URL in the email, and it has to be caught there.
If your current threat intel feed didn’t have marketing-partner-join[.]com on day two, it’s worth asking what else it’s missing. Request a free API trial → or investigate any domain yourself at threatYeti.com.
Indicators of Compromise
The following hostnames were active as of April 18, 2026. All carry a risk rating of 7.60 on aM Intelligence™.
base.marketing-partner-join.com
care.marketing-partner-join.com
engine.marketing-partner-join.com
guide.marketing-partner-join.com
linkhub.marketing-partner-join.com
manage.marketing-partner-join.com
marketing-partner-join.com
member.marketing-partner-join.com
member01.marketing-partner-join.com
member02.marketing-partner-join.com
member13.marketing-partner-join.com
member21.marketing-partner-join.com
member24.marketing-partner-join.com
member27.marketing-partner-join.com
panel.marketing-partner-join.com
prime.marketing-partner-join.com
securex.marketing-partner-join.com
service.marketing-partner-join.com
shieldx.marketing-partner-join.com
support.marketing-partner-join.com
support03.marketing-partner-join.com