Maltego is a popular intelligence platform used by professionals in the cybersecurity, law enforcement and trust and safety industries. Common use cases for maltego include persons of interest investigations, security research and cyber threat investigations.
At its core, Maltego enables the visualization and graphic relationship mapping of digital entities. This speeds up investigations and analyses by bringing disparate data sources into a unified platform.
alphaMountain’s domain and IP threat intelligence is integrated with Maltego to enable cyber threat researchers to move confidently and conclusively through their investigations.
Getting started
To get started with Maltego and alphaMountain, all you need is the latest version of the Maltego application on your PC or Mac. Note that there are several versions of Maltego available. For individuals there is the free Maltego CE (community edition) and the paid version, Maltego One. Pick the version that is right for you based on your use case.
Once you have Maltego installed on your machine, there are two basic concepts you’ll want to get your head around.
Basic concepts in Maltego
Entities
Think of entities as things that you want more information about. These could be a person, a device, a social network or a number of other things. Check out the Maltego docs for entities to learn more.
Transforms
Think of transforms as searches or queries you can make on an entity to “transform” its basic entity type into other, more-granular information such as transforming a website URL into an IP address. With Maltego’s free community edition, you get 25 free transform runs per month.
When you’ve run out of those credits, you can also bring your own key by requesting an alphamMountain API key directly from us.
Graphs
Graphs are the workspaces for projects. This is the canvas of your investigation where you will drag new entities from the entities palette sidebar and apply transforms that will result in new points on the graph.
Let’s dive into how you can use alphaMountain right away to enrich a threat investigation.
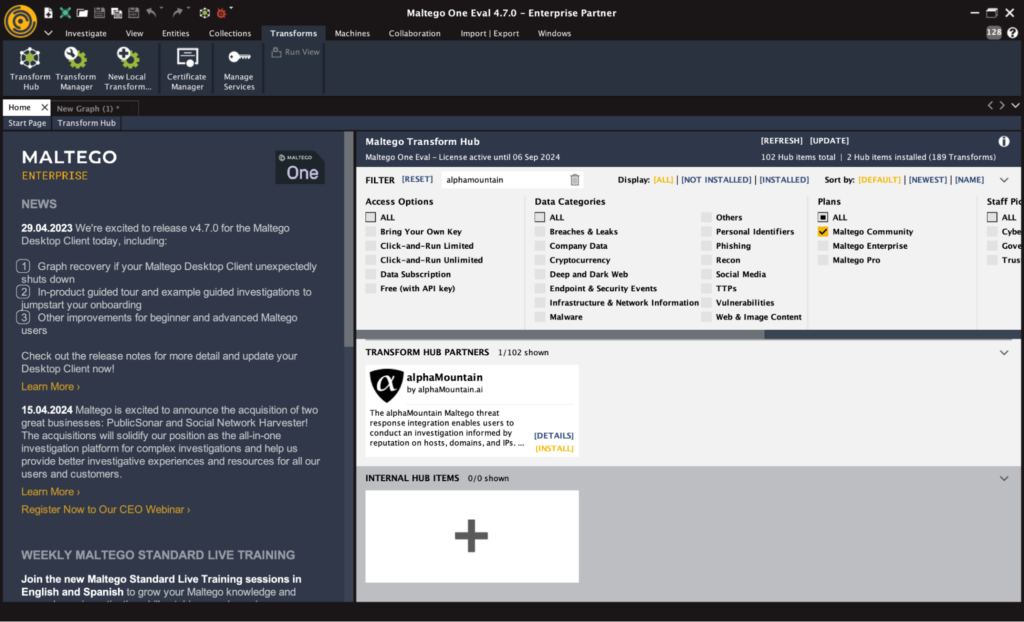
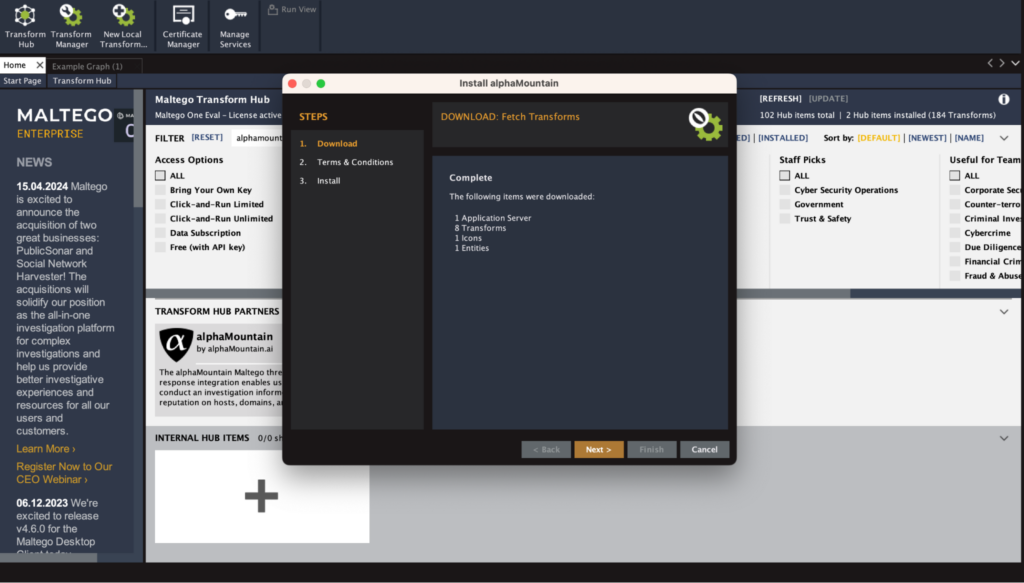
Install the alphaMountain Transform
- Go to the Transforms tab and click Transform Hub
- Type ‘alphaMountain’ in the filter bar
- Hover over the alphaMountain card and click ‘Install’
- Click ‘Yes’, click ‘Next’ and follow the instructions
- You’re done!
Enrich investigations with alphaMountain
You probably have a much more in-depth use case, whether it’s security research, incident response or a threat investigation, but here is a quick example of how you can use alphaMountain to enrich your investigations by bringing a real-time URL risk rating and categorization into your reports.
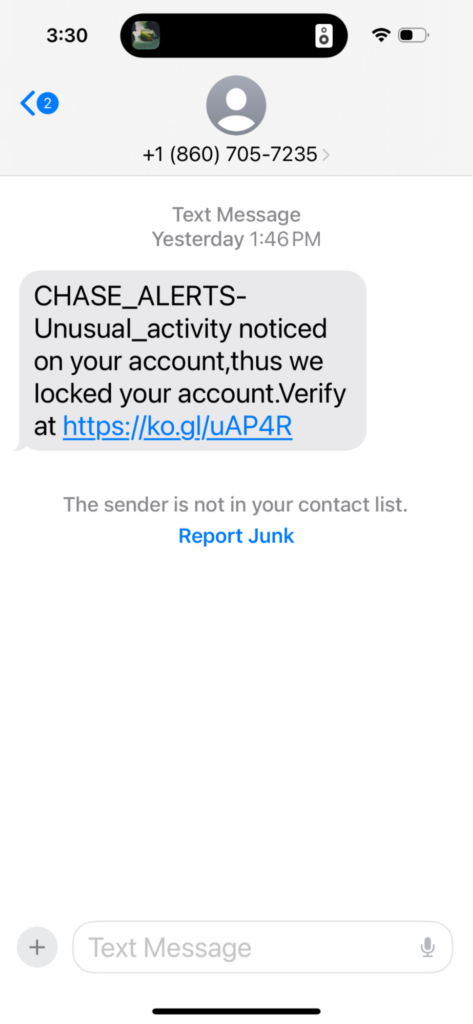
Here is an unsolicited SMS message we recently received from a number purporting to be from Chase bank:
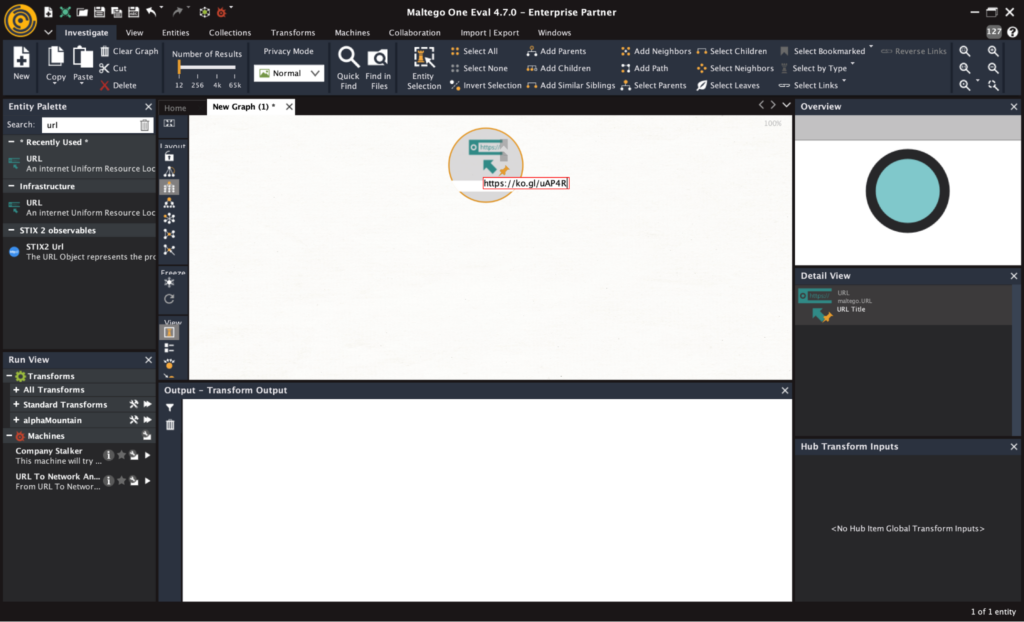
The first thing to do is to drag the Domain entity into the graph, then double click on the default value and enter the URL from this message: <ko.gl/uAP4R> and press Enter.
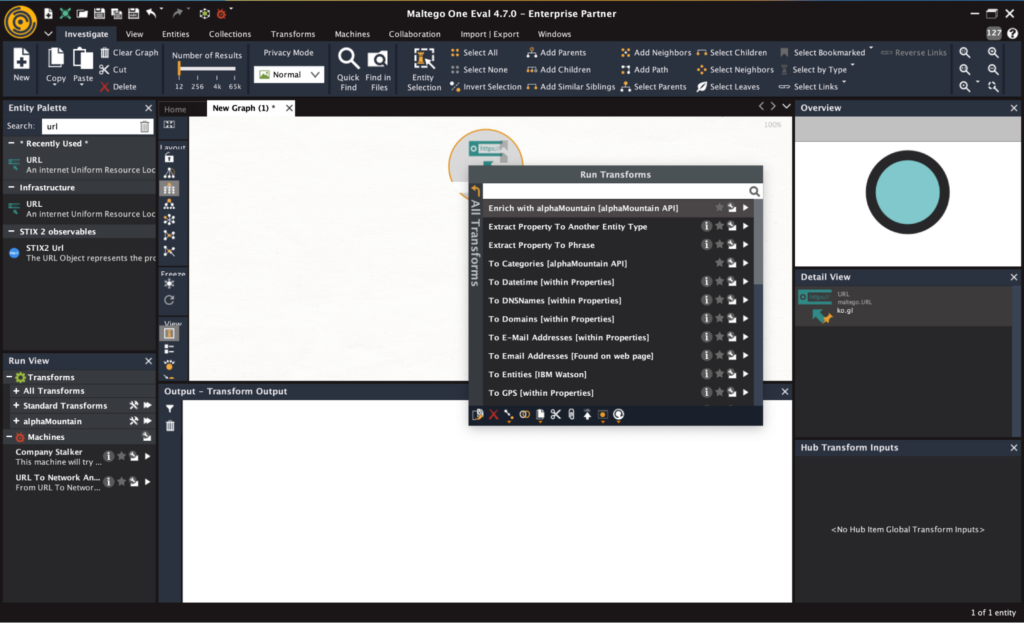
Next, right click on the entity and select ‘Enrich with alphaMountain.”
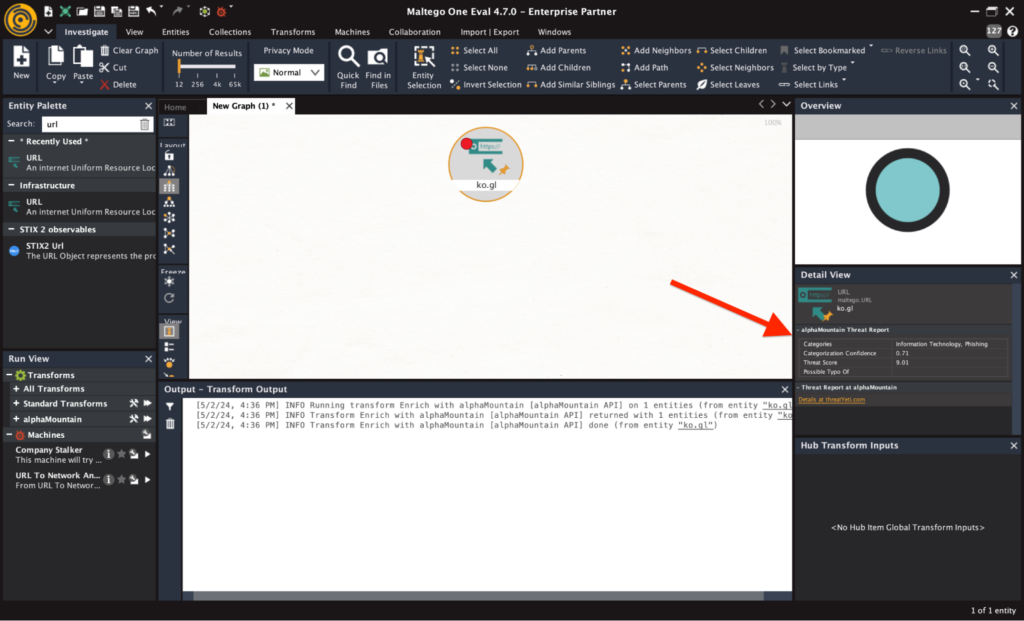
You’ll see the threat score returned in the Detail View on the right. In this case, we can see it’s a high risk domain with a threat score of 9.01
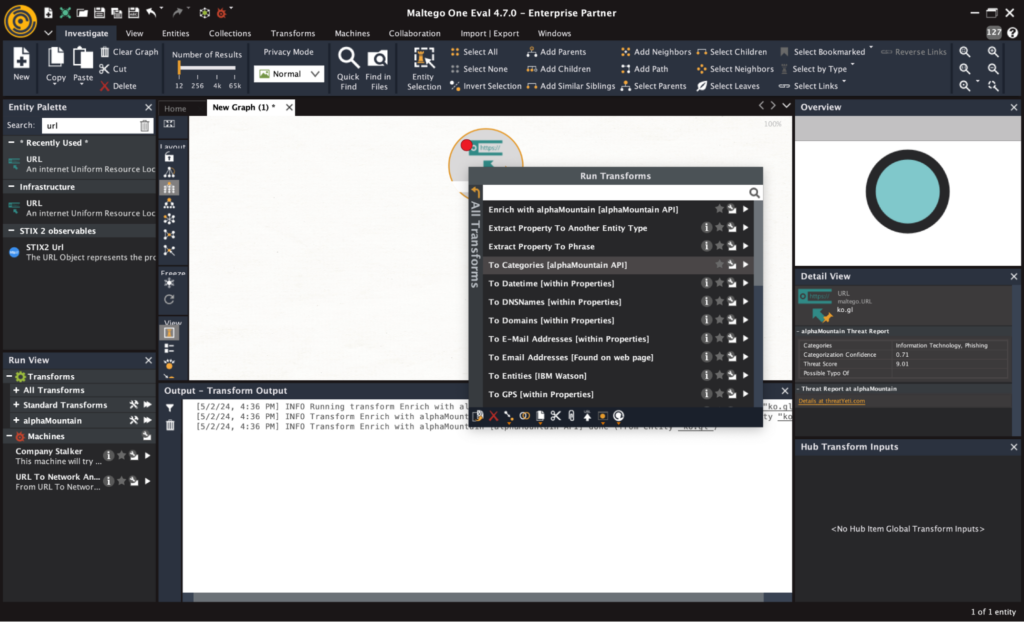
You can also graph the categories into which the domain is classified by right clicking on the URL entity and selecting ‘To Categories.’
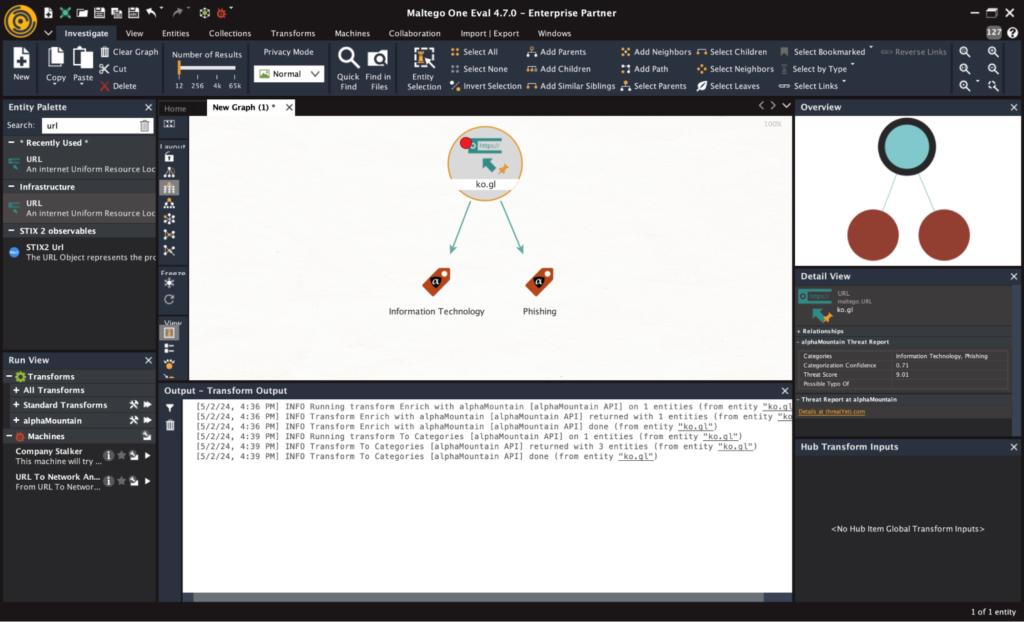
Now you will see the categories returned by alphaMountain in the graph for this particular URL. In this case, the categories are “Information Technology” and “Phishing.”
It’s clear now from the alphaMountain categories that this SMS message was a phishing attempt by a threat actor. Naturally, the SMS was deleted and reported, eliminating the threat.
Save time in your own investigations by integrating alphaMountain’s URL threat intelligence and category API.
alphaMountain API Options
You can request your free trial key at any time by visiting our threat intelligence API page. Starting a free trial is a great way to explore and experiment inside Maltego so you can get a feel for how fresh threat intelligence can lead you to confident conclusions in your investigations.